Guest post originally published on the Nirmata blog by Jim Bugwadia
The Cloud Native Computing Foundation (CNCF) held the first ever standalone Cloud Native Security Conference in Seattle on February 1st and 2nd. Here are some of my highlights from this event.

As the adoption of cloud-native technologies like containers and Kubernetes has grown, security remains an active topic. With prior KubeCons, SecurityCon was a co-located event. However, due to high interest and large number of topics, the event quickly became too large and now is its own separate conference.
While there were several interesting sessions, often multiple at the same time, here I have focused on the ones related to Kubernetes policy and governance.
How Yahoo secures its software supply chain
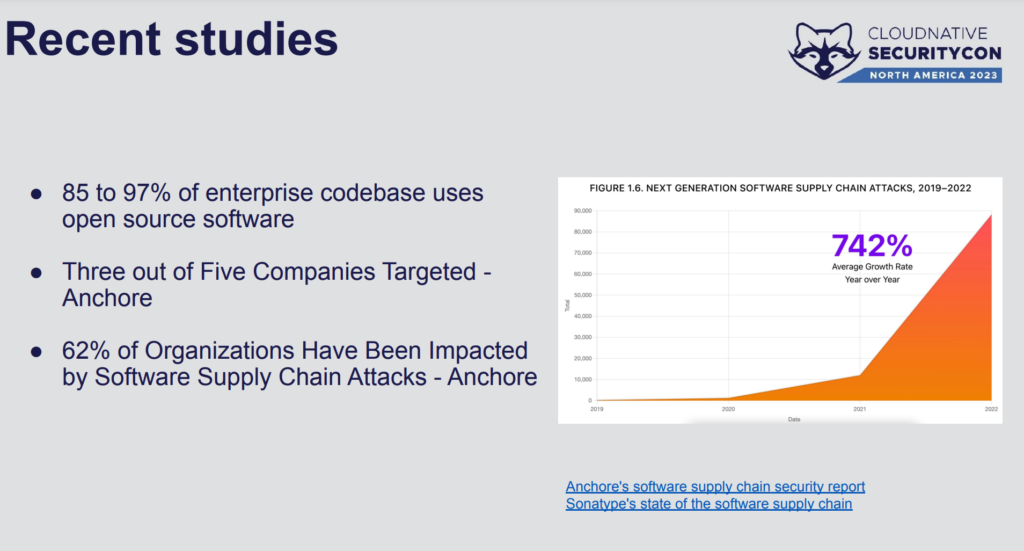
Hemil Kakadia and Yonghe Zhao from Yahoo provided a deep-dive on their journey to securing their software supply chain, across 700+ Kubernetes clusters and 5K+ daily published container images. They started with a look at why software supply chain security is important, highlighting that a recent survey showed that three out of five companies have been targeted in supply chain attacks.
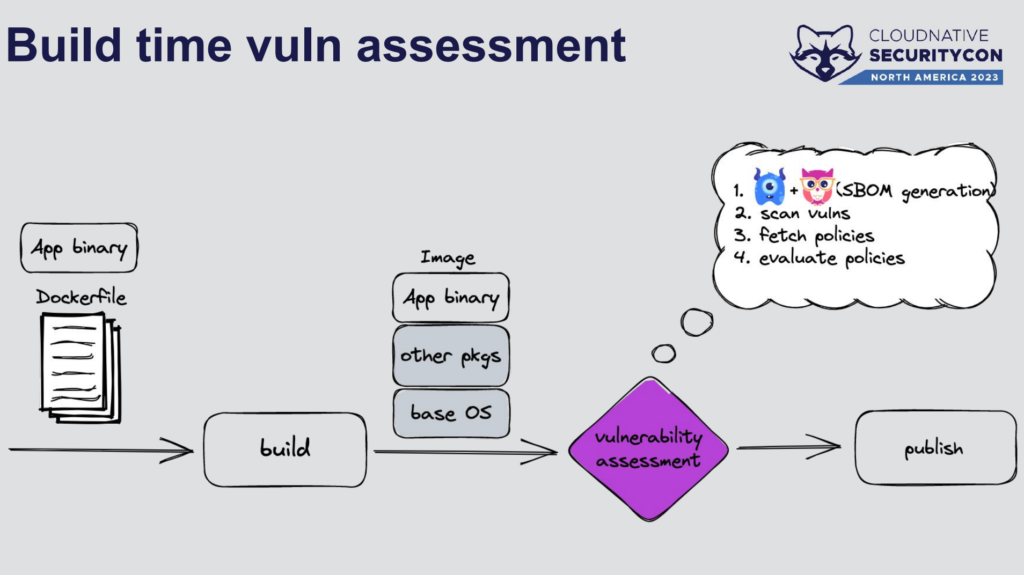
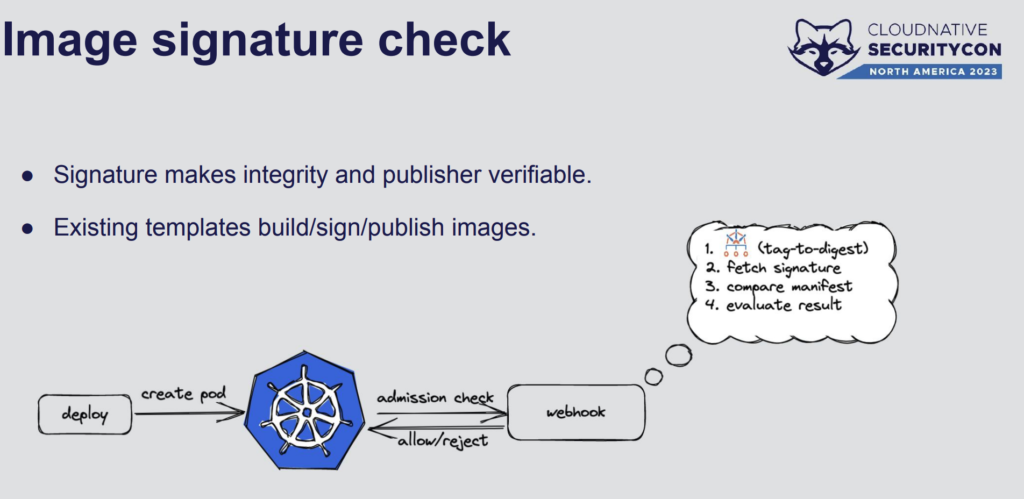
They use Sigstore Cosign to sign their images and Kyverno to verify images. They collect metadata from tools like Grype and Syft during the build phase, and publish this information to an OCI image registry so it can be verified during deployment.
They currently use multiple webhooks. Grafeas is used for the metadata checks and Kyverno for the image signature checks. They plan to explore consolidating on Sigstore and Kyverno in the future.
One interesting and practical thing they do is run an “image freshness” check, where a Kyverno policy checks for images that have not been updated in a while.
The policy is available in the Kyverno policy library at: https://kyverno.io/policies/other/block_stale_images/block-stale-images/.
The Yahoo journey to secure software supply chains continues to evolve as cloud-native projects mature and offer additional capabilities. This will be interesting to follow and I am looking forward to more presentations from the team!
The full video is available at How to Secure Your Supply Chain at Scale – Hemil Kadakia & Yonghe Zhao, Yahoo
The evolution of Infrastructure as Code
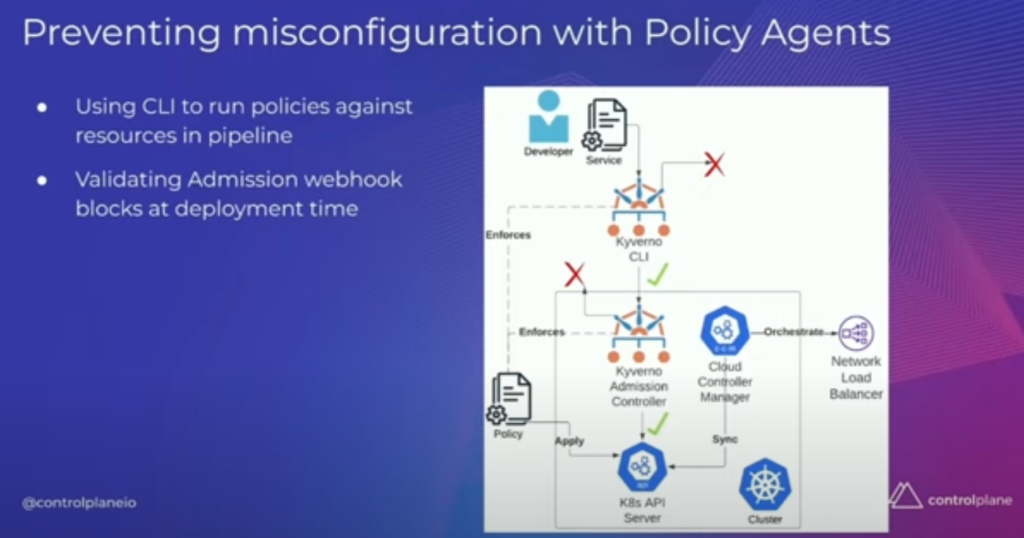
In the session, “Avoiding IAC Potholes with Policy + Cloud Controllers” Andrew Martin from Controlplane explained why traditional approaches for IaC, where policy is applied prior to provisioning, do not work well for cloud-native technologies that enable developer self-service.
For example, in Kubernetes new infrastructure may be dynamically requested by developer actions such as requesting a Kubernetes LoadBalancer service as part of a workload. In addition, cloud controllers from major providers and CNCF projects like Crossplane allow cloud infrastructure e.g. an AWS S3 bucket, to be provisioned as part of the workload.
This dynamic and self-service nature of cloud native requires new ways of enabling policy and governance. Cloud-native policy controllers apply policy to any Kubernetes resource in the pipeline, at admission controls, and via runtime scanning are required.
Andy also demonstrated a solution built by Rowan Baker that showcased how policy-based compliance can be automated. This solution used Lula, a tool developed by Brandt Keller at Defense Unicorns, that maps Kyverno policies to the NIST Open Security Controls Assessment Language (OSCAL) specification.
Checkout the full video at: Avoiding IAC Potholes with Policy + Cloud Controllers – Andrew Martin, ControlPlane
What’s next for software supply chain security
In the Day 2 keynotes, Brandon Lum from Google, shared the work his team and the SIG Security team is doing for software supply chain security.
Brandon covered supply chain security from a producer and consumer perspective. He first introduced the projects and tools that establish trust and produce software supply chain artifacts. Next, he covered tools that consume this data.
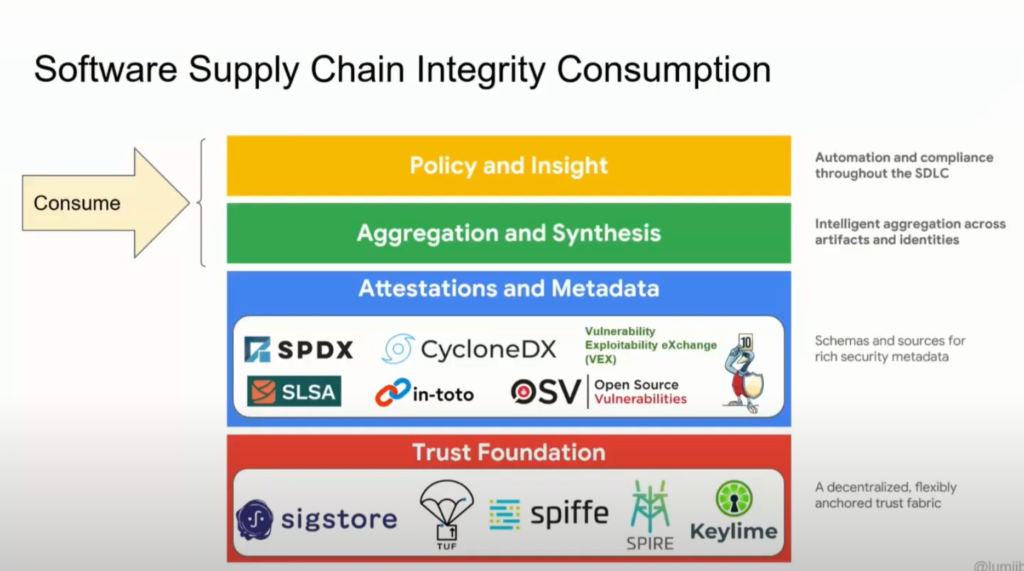
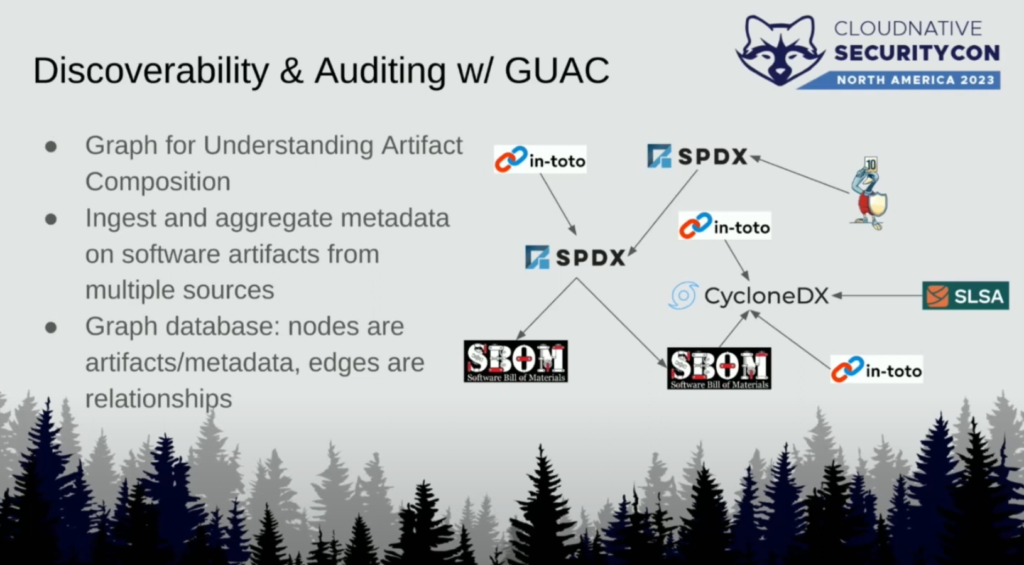
One type of consumption is aggregating supply chain data. This is what a new project called GUAC which is an acronym for Graph for Understanding Artifact Composition does (more on this project in the next talk!)
Policy engines, like the CNCF projects Kyverno and OPA/Gatekeeper, are used to consume artifacts and metadata and enforce security checks:
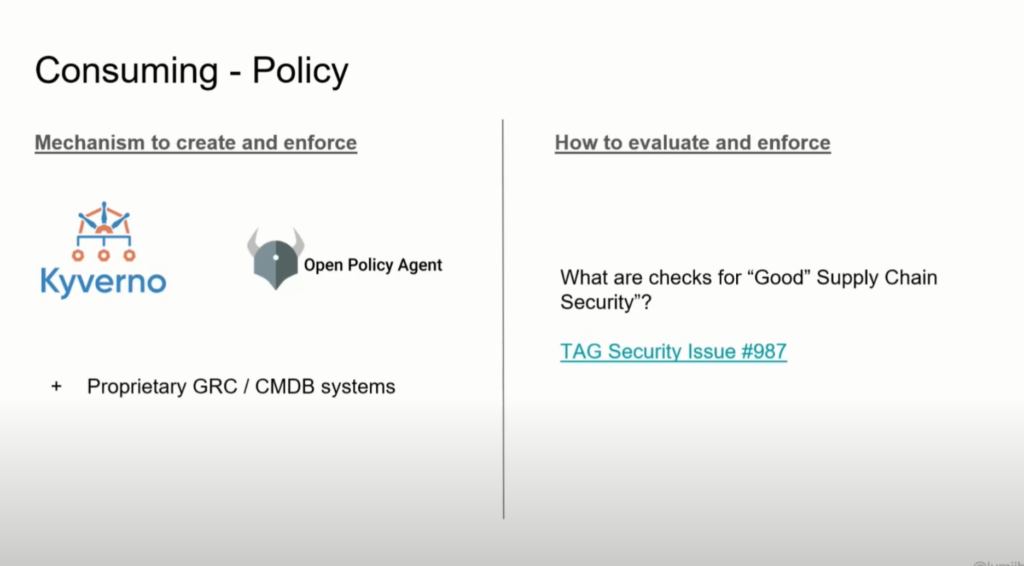
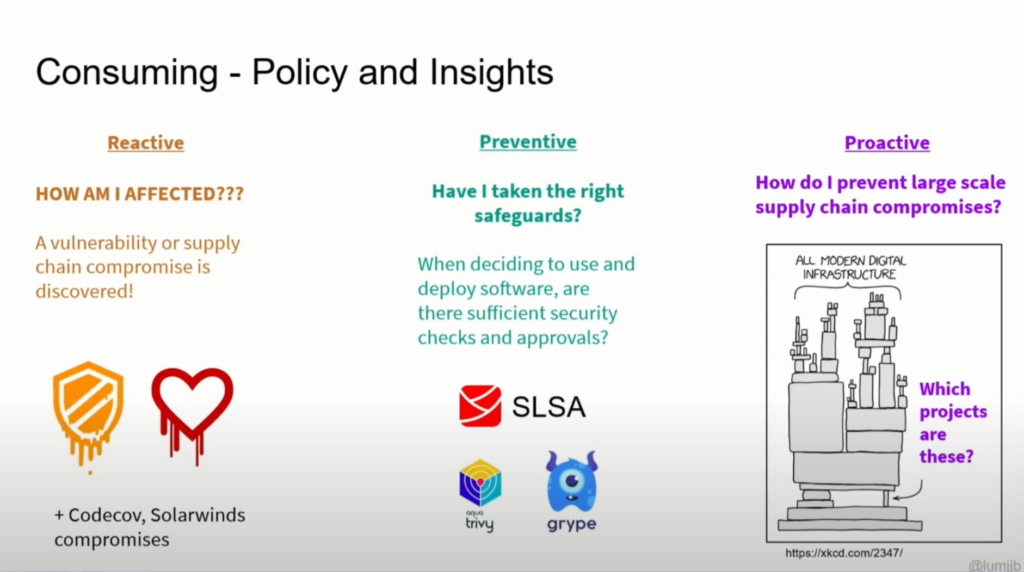
Brandon discussed three different types of policies that the Supply Chain Working Group is defining:
- Reactive: to query if a system is impacted for a known vulnerability
- Preventive: to block non-compliant artifacts based on inspection of data
- Proactive: to prevent the next compromise via scorecards or other attributes to be defined
If you are interested in software supply chain security (and you should be!) I highly recommend checking out Brandon’s keynote:
Keynote: The Next Steps in Software Supply Chain Security – Brandon Lum, Software Engineer, Google
SLSA and GUAC
In a session later that day, Ian Lewis from Google presented a deep dive into some of the topics that Brandon introduced in his keynote. Ian covered an emerging compliance standard and toolset called Supply Chain Levels for Software Artifacts (SLSA) being developed by the OpenSSF, and the GUAC project for mapping relationships across supply chain artifacts.
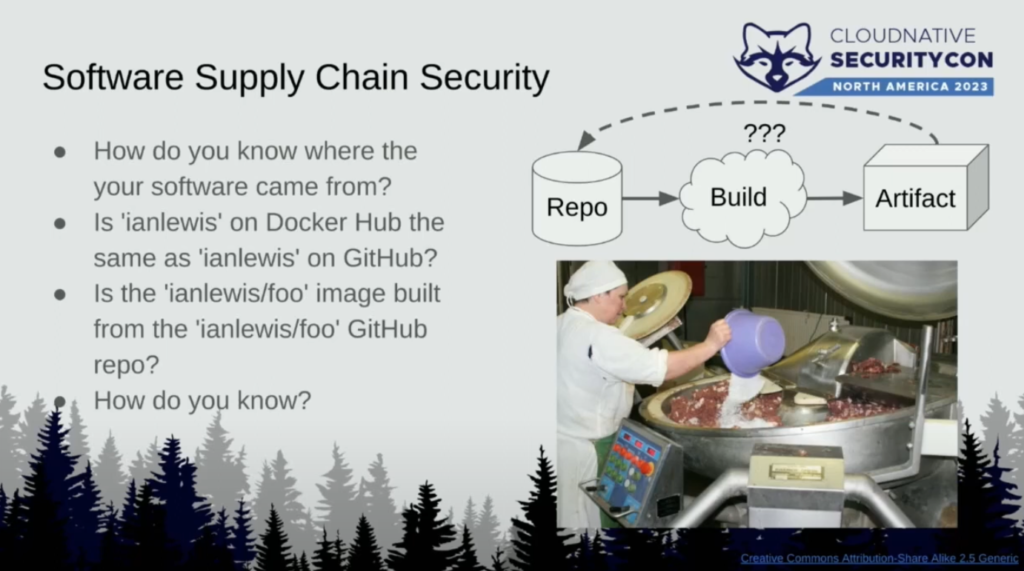
Ian kicked off his talk with a great description of the challenges in software supply chain security:
Ian then described the different levels of SLSA compliance, and then described tooling like SLSA generators that produce provenance data in a CI system, and SLSA verifiers that can be used to locally verify the provenance data.
Ian showed the current state of supply chain verification with projects like Kyverno and the Sigstore policy controller, where policies can verify attestations (signed metadata) created during build time.

Ian then discussed what new and emerging tools like GUAC will enable for richer policy decisions, including using proactive analysis.
Watch the session at: Spicing up Container Image Security with SLSA & GUAC – Ian Lewis, Google
Summary
While a major focus of the keynotes and sessions was on new areas, like eBPF based security and observability, and software supply chain security, it was interesting that most end user conversations I had were on topics such as Kubernetes pod security, multi-tenancy, and best practice policies. Hence its important for end users to not get carried away with, or be intimidated by, emerging technologies but focus on starting with the basic building blocks for cloud native security and automation.
Cloud native technologies introduce new layers to secure and manage. However, what is exciting about cloud native technologies is that they also offer a chance to transform and improve security processes, in an open and flexible manner to enable better end user experiences with improved security, autonomy across roles, and agility.
Overall the energy at CNSCon was great and the cloud-native community is truly building new and innovative ways of securing our future!
If you are interested in learning more about Kyverno and how it addresses Kubernetes security and automation, checkout these links: