The Cilium project is excited to announce the general availability of Cilium 1.12.
Cilium is well known as the de-facto standard for cloud native networking and security, adopted by companies like Adobe, Bell Canada, and IKEA as well as many managed Kubernetes platforms including products from Google Cloud and AWS. Major features in the 1.12 release of Cilium have been contributed by Datadog, F5, Form3, Isovalent, Microsoft, Seznam.cz, The New York Times, and many more contributors.
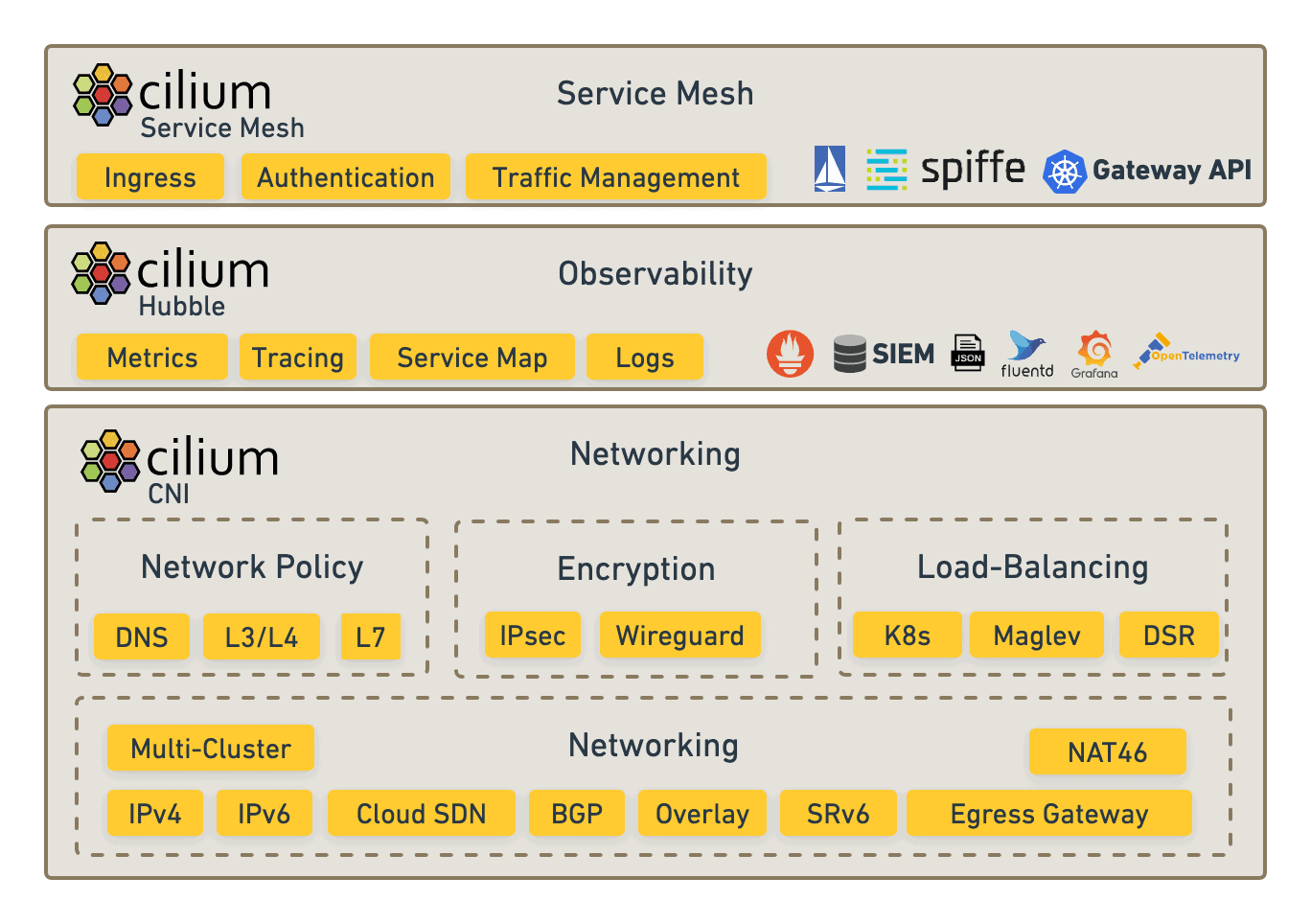
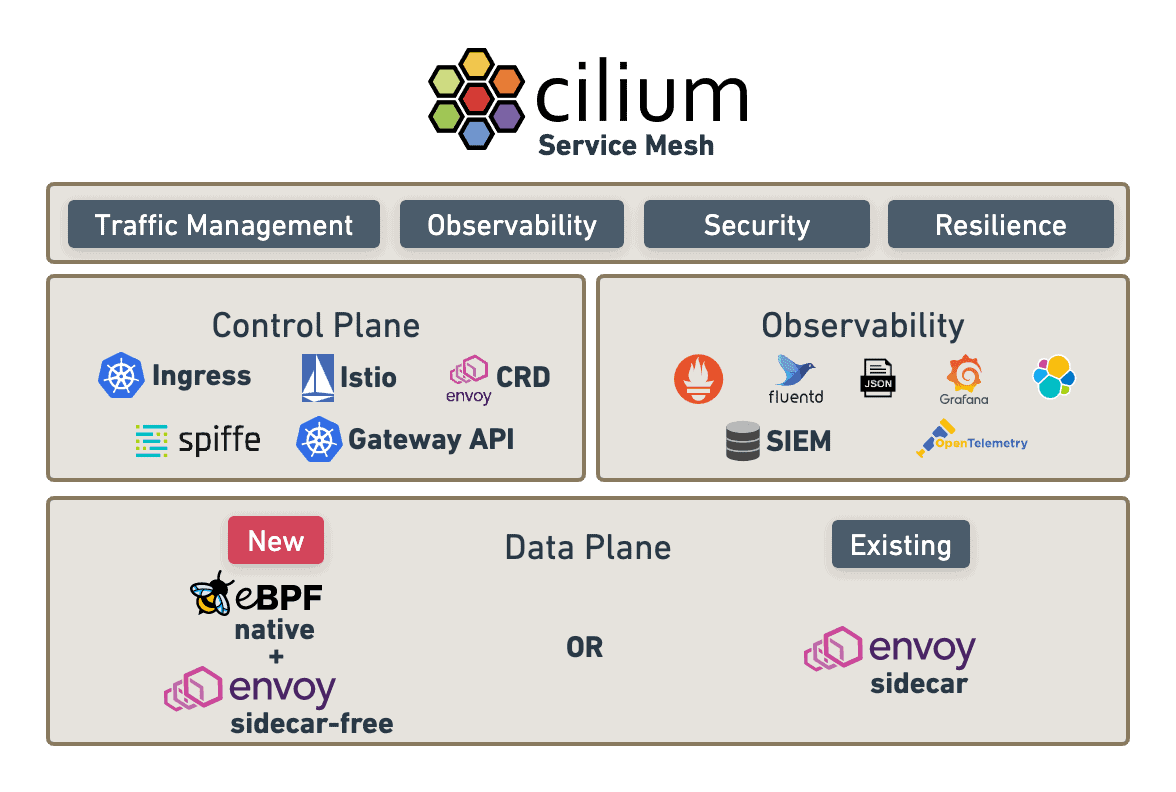
With the release, Cilium has introduced Cilium Service Mesh, a major new open source entrant into the service mesh category, and the first service mesh that gives enterprises the flexibility to run service mesh in a sidecar model or a sidecar-less model and with a broad choice of different control planes. In addition, this release has also introduced a fully compliant Kubernetes Ingress controller directly integrated into Cilium.
A Kubernetes-Native Service Mesh with Optional Sidecars
The vision for Cilium Service Mesh is a service mesh built using native Kubernetes resources, just like Cilium’s ClusterMesh uses Kubernetes Services and NetworkPolicy to perform multi-cluster connectivity. Today we are announcing the availability of the first stable release of a new exciting option to run Cilium as a service mesh completely without sidecars while supporting a variety of different control plane options. It complements the already existing sidecar-based Istio integration that has been available as part of Cilium so far.
With this, we are aiming to reduce complexity and overhead in the service mesh layer by introducing choice for our users. Users can decide based on their unique needs whether to run a service mesh with or without sidecars based on what best meets the needs and requirements of their platform.
“Cilium Service Mesh is all about choice,” said Thomas Graf, Cilium creator and Isovalent CTO and co-founder. “Enterprises want the ability to choose sidecars or sidecar-less, and they want a high-performance data plane powered by eBPF and Envoy that allows them to choose the best control plane for their use case. By combining the well proven Envoy proxy with kernel-level eBPF technology, Cilium Service Mesh is giving enterprises the best possible service mesh performance, while also allowing them to choose between a sidecar or sidecar-less model.”
With the release, Cilium Service Mesh also introduced CiliumEnvoyConfig (CEC), its low level abstraction for programming Envoy proxies directly with a new Kubernetes Custom Resource (CRD) for advanced L7 use cases to make the full feature set of Envoy available to all users. Over the next releases, Cilium Service Mesh will add support for additional service mesh control planes, starting with the Gateway API and its GAMMA initiative for Service Mesh use cases. This will make the Cilium Service Mesh data plane compatible with the service meshes such as Istio which are already migrating to Gateway API.
Other Cilium 1.12 Major Features
In addition to Cilium Service Mesh, Cilium 1.12 ships with many new features and enhancements, including:
- Fully Compliant Ingress Controller – Besides the new sidecar-free Service Mesh option, Cilium 1.12 also features a fully compliant Kubernetes Ingress controller directly embedded in Cilium. It’s powered by Envoy with eBPF used to secure it and provide visibility around it.
- ClusterMesh enhancements including service affinity — In Cilium 1.12, ClusterMesh can treat services running on multiple clusters as a single global service with affinity taken into account. With service affinity, services can be configured to prefer endpoints in the local or remote cluster, if endpoints in multiple clusters are available.
- Egress Gateway and additional support for external workloads — Egress Gateway, previously introduced as a beta feature, is now stable. Cilium allows you to forward connections to external, legacy workloads through specific Gateway nodes, masquerading them with predictable IP addresses to allow integration with legacy firewalls that require static IP addresses. When combined with ClusterMesh, external workloads can support requests that ingress on other clusters in the mesh.
- Cilium Tetragon Released — Cilium’s new Tetragon component enables powerful real-time, eBPF-based Security Observability and Runtime Enforcement. Tetragon detects and is able to react to security-significant events, such as process execution events, system call activity and I/O activity including network & file access. Watch the Cilium community video on “Security Observability with eBPF and Tetragon” for more information.
- Additional Cilium Enhancements in 1.12 — additional Network Visibility controls, ability to run Cilium as non-privileged containers, dynamic allocation of pod CIDRs, IPv4/IPv6 NAT, AWS ENI prefix delegation, and many more.